Ideal Practices for Implementing Universal Cloud Storage Space Solutions in a Remote Work Atmosphere
As companies shift to remote work designs, the implementation of cloud storage space services is extremely important in ensuring availability, protection, and cooperation among dispersed teams. The successful implementation of these solutions calls for mindful factor to consider of different aspects, consisting of information organization approaches, gain access to control systems, backup protocols, assimilation with collaboration tools, and robust security procedures.
Information Organization Approaches
One fundamental facet of effective information monitoring in a remote workplace is the implementation of structured and instinctive information organization strategies. Appropriate information company is necessary for making certain that info is quickly obtainable, searchable, and safeguard. In a remote job setup, where employees may not have prompt physical accessibility to shared drives or declaring closets, a well-thought-out information company system comes to be even extra critical.
Effective information company strategies typically include categorizing info based on significance, developing sensible folder structures, and implementing calling conventions that make it straightforward to recognize and recover data. Making use of metadata tags can likewise boost the searchability of information, allowing users to swiftly find the info they need without squandering time checking out various folders.
Accessibility Control and Permissions
In a remote job atmosphere, applying robust gain access to control and authorization devices is critical to guarding sensitive information and making sure regulatory compliance. Additionally, executing file encryption for information at remainder and in transportation improves information defense. By enforcing strict access control procedures and authorizations, companies can minimize safety threats and preserve data integrity in a remote job setting.
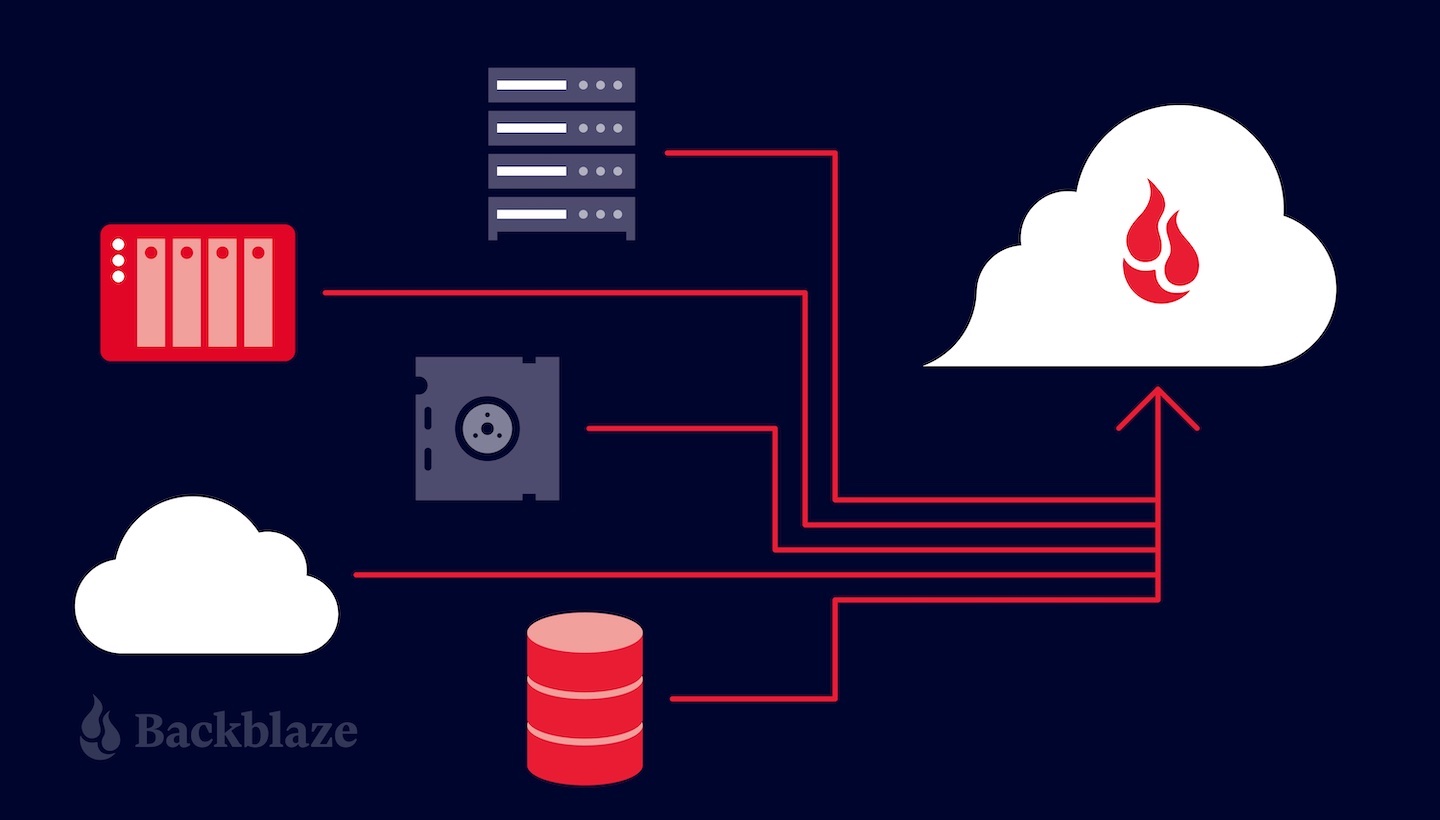
Back-up and Recuperation Protocols
Executing robust backup and healing procedures is important for making sure data resilience and continuity in a remote work environment. In a distributed setup, where workers are functioning from various locations, the danger of information loss due to human mistake, cyber dangers, or technical failures is enhanced (Universal Cloud Storage).
Organizations should consistently examine their backup systems to ensure they can promptly recover data when required. Having a well-defined healing strategy that details the steps to be taken in different circumstances and designating responsible people for performing the plan can better boost data recuperation capabilities.
Partnership Equipment Combination
Making use of collaboration devices that view website sync with cloud storage space services improves and simplifies workflows efficiency. For instance, employee can all at once edit files stored in the cloud, track modifications, and provide feedback in see real-time. This level of assimilation minimizes version control issues and promotes seamless partnership.
Furthermore, incorporated partnership tools typically use additional functions like task project, due date monitoring, and progression surveillance, which are essential for remote group management. These tools not just assist in communication but additionally promote liability and openness within the team, eventually bring about enhanced performance and task results in a remote job setup.
Safety And Security Steps and Conformity
Provided the important duty that partnership devices play in enhancing remote group communications, ensuring robust security measures and compliance procedures is paramount to secure sensitive information and preserve governing requirements. In a remote workplace where data is accessed and shared throughout numerous gadgets and places, executing strong security procedures is essential to stop unauthorized gain access to, data breaches, and compliance infractions.
To boost safety and security, companies must apply security protocols, multi-factor authentication, and regular security audits to identify and deal with susceptabilities. Furthermore, developing clear policies pertaining to data gain access to, sharing permissions, and device management can assist minimize dangers connected with remote job techniques.
Conformity with policies such as GDPR, HIPAA, or industry-specific standards is important to stay clear of legal ramifications and secure client trust. Organizations ought to stay informed concerning progressing conformity requirements, train employees on data defense finest methods, and on a regular basis upgrade protection procedures to line up with altering guidelines.
Conclusion
To conclude, carrying out global cloud storage services in a remote job setting needs cautious factor to consider of data organization methods, accessibility control and permissions, backup and recovery methods, collaboration tools integration, and safety and security measures and conformity. By adhering to best practices in these anchor locations, companies can ensure that their remote job environment is efficient, protected, and effective. LinkDaddy Universal Cloud Storage. It is important to focus on these elements to efficiently execute cloud storage solutions in a remote work setup
One basic element of reliable data administration in a remote work environment is the implementation of instinctive and organized data organization strategies. In a remote work setting, where workers might not have immediate physical accessibility to shared drives or filing cabinets, a well-balanced data organization system comes to be even a lot more vital.
Furthermore, carrying out security for data at remainder and in transportation enhances data protection. Universal Cloud Storage Press Release. By applying stringent gain access to control procedures and authorizations, companies can minimize safety risks and preserve information stability in a remote work setup
In final thought, carrying out global cloud storage solutions in a remote job environment calls for cautious factor to consider of information organization approaches, accessibility control and approvals, backup and recovery protocols, partnership tools assimilation, and safety measures and conformity.